New Adware "BeiTaAd" Found Within Popular Applications in Google Play
Over the past year, roughly 440 million Android users have downloaded apps from the official Google Play Store that contained an advertising library that showed out-of-app ads.
This advertising library, called the BeiTaPlugin, was found embedded in 238 applications, Kristina Balaam, Security Intelligence Engineer at Lookout said in a report.
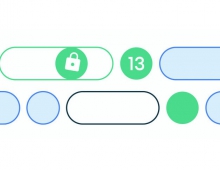
BeiTaAd forcibly displays ads on the user’s lock screen, triggers video and audio advertisements even while the phone is asleep, and displays out-of-app ads that interfere with a user’s interaction with other applications on their device.
Lookout reported the malicious functionality to Google and the BeiTaPlugin has now been removed from all the affected apps on the Play store. Cumulatively, these applications amount to over 440 million installations, making this family unique in its prevalence and the level of obfuscation used to hide the plugin’s existence.
"While the vast majority of free mobile applications monetize their apps through Ad SDKs or plugins, the persistence of the advertisements in this particular family and the lengths to which the developer went to hide its existence make the BeiTaPlugin concerning," Balaam said.
All of the apps released with BeitaPlugin were published by mobile internet company, CooTek, founded in 2008 in Shanghai. CooTek became listed on the NYSE in 2018 and is best known for its popular keyboard app, TouchPal. The BeiTaPlugin package, com.cootek.beita.plugin, is unsurprisingly bundled within TouchPal as well as numerous add-ons to their popular TouchPal keyboard, and several very popular health and fitness apps.
While out-of-app ads are not particularly novel, those served by this plugin render the phones nearly unusable. Users have reported being unable to answer calls or interact with other apps, due to the persistent and pervasive nature of the ads displayed. These ads do not immediately bombard the user once the offending application is installed, but become visible at least 24 hours after the application is launched. For example, obtrusive ads did not present themselves until two weeks after the application, Smart Scan (com.qrcode.barcode.reader.scanner.free), had been launched on a Lookout test device.
Users have documented similar experiences on an Android forum discussion spanning several months, as well as in reviews left on the applications’ Google Play pages.
The BeiTa plugin has been refactored several times since its initial release in early 2018. In more recent iterations, the BeiTa plugin is renamed to the innocuous, icon-icomoon-gemini.renc, and is encrypted using Advanced Encryption Standard (AES). Icomoon is an application that provides vector icon packs for designer and developer use. One Icomoon-compatible icon pack is named Gemini. Malware authors commonly employ this technique of renaming executable files to other file types (pdf, jpg, txt) to hide malicious assets in plain sight.
The loaded plugin is never installed to the device. Therefore, it is not listed as an installed package nor is it possible to simply uninstall the plugin without uninstalling the carrier application.
As of May 23rd, 2019, the 230+ affected applications on Google Play have either been removed or updated to versions without the BeiTa Plugin.