Apple Will Not Unlock iPhones Even For the FBI, But User's Backup Data is a Different Story
While Apple says it won't decrypt any iPhone for anyone including the U.S federals, the company has left the door "open" for its iCloud servers.
Apple designs iPhones so that no one—not even the company—can unlock devices without a user’s consent. The U.S. government objects, saying it wants a backdoor to the phones for use in extreme cases.
Reuters reported this week that Apple had abandoned a plan two years ago to strengthen encryption on the personal data it holds on its servers. Had Apple gone through with the changes, it’s possible the Federal Bureau of Investigation would have even less information about the digital life of the Saudi Air Force member who killed three people at a naval base in Pensacola, Florida, in December. So Apple’s decision not to add end-to-end encryption for iCloud backups maintains that side door.
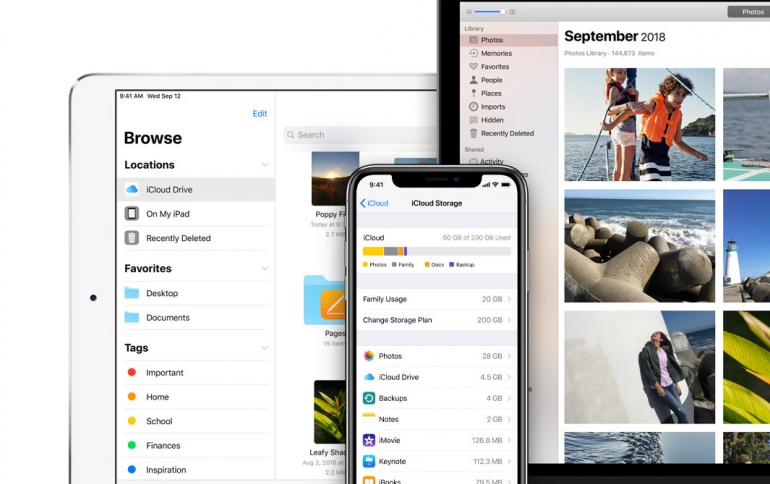
Apple encourages iPhone users to back up their information automatically to iCloud. That means that in many cases, there’s a copy of all that sensitive and encrypted information parked on Apple’s servers. Although users' data are "protected" with encryption from potential intruders to Apple's servers, Apple is able to decrypt it. If faced with a warrant, Apple is sometimes willing to turn that key to help law enforcement.
Users of Apple's are able to opt-out from iCloud backups for certain apps, or turn it off altogether. But there’s still plenty information there, and it appears to be accessible. When the Trump administration began attacking Apple for being unhelpful in the Pensacola investigation, Apple said it had already shared the suspect's iCloud data.





















