Google To Start Notifying Users Affected By The DNSChanger Malware
Google will notify roughly half a million people whose
computers or home routers are infected with a
well-publicized form of malware known as DNSChanger.
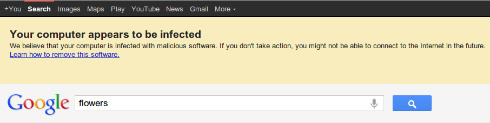
Google will start showing warnings via a special message
that will appear at the top of the Google search results
page for users with affected devices.
The Domain Name System (DNS) translates familiar web address names like google.com into a numerical address that computers use to send traffic to the right place. The DNSChanger malware modifies DNS settings to use malicious servers that point users to fake sites and other harmful locations. DNSChanger attempts to modify the settings on home routers as well, meaning other computers and mobile devices may also be affected.
Since the FBI and Estonian law enforcement arrested a group of people and transferred control of the rogue DNS servers to the Internet Systems Consortium in November 2011, various ISPs and other groups have attempted to alert victims. However, many of these campaigns have had limited success because they could not target the affected users, or did not appear in the user?s preferred language (only half the affected users speak English as their primary language). At the current disinfection rate hundreds of thousands of devices will still be infected when the court order expires on July 9th and the replacement DNS servers are shut down. At that time, any remaining infected machines may experience slowdowns or completely lose Internet access.
Google expects to notify over 500,000 users within a week.
The Domain Name System (DNS) translates familiar web address names like google.com into a numerical address that computers use to send traffic to the right place. The DNSChanger malware modifies DNS settings to use malicious servers that point users to fake sites and other harmful locations. DNSChanger attempts to modify the settings on home routers as well, meaning other computers and mobile devices may also be affected.
Since the FBI and Estonian law enforcement arrested a group of people and transferred control of the rogue DNS servers to the Internet Systems Consortium in November 2011, various ISPs and other groups have attempted to alert victims. However, many of these campaigns have had limited success because they could not target the affected users, or did not appear in the user?s preferred language (only half the affected users speak English as their primary language). At the current disinfection rate hundreds of thousands of devices will still be infected when the court order expires on July 9th and the replacement DNS servers are shut down. At that time, any remaining infected machines may experience slowdowns or completely lose Internet access.
Google expects to notify over 500,000 users within a week.