Researchers to Challenge Tesla Model 3, Web Browsers and More at Pwn2Own Contest
Zero Day Initiative's Pwn2Own hacking contest returns to Vancouver this year, and the research community will try to identify security vulnerablilities in Tesla Model 3 and web browsers.
The contest is rewarding security researchers for privately disclosing vulnerabilities.
Last year, the Zero Day Initiative raised more than a few eyebrows by partnering with Tesla to include a Model 3, the best-selling car in its class in the U.S., as a target, and ended up awarding the car to two talented researchers.
This year, Tesla returns to the contest. Driving off with a new Model 3 will be a harder challenge this year, which means the potential rewards will be much higher as well. Microsoft also returns as partner and VMware returns as a sponsor with their somewhat more traditional Pwn2Own targets. More than $1,000,000 USD in cash and prizes are available to contestants, including the new Tesla car.
As usual, the Pwn2Own will be held at the CanSecWest conference, which occurs on March 18-20 of this year. Here’s a look at all six of the categories available for this contest:
- Automotive Category
- Web Browser Category
- Virtualization Category
- Enterprise Applications Category
- Server-Side Category
- Local Escalation of Privilege Category
Pwn2Own is crowning a Master of Pwn. Since the order of the contest is decided by a random draw, contestants with an unlucky draw could still demonstrate fantastic research but receive less money since subsequent rounds go down in value. However, the points awarded for each successful entry do not go down. Someone could have a bad draw and still accumulate the most points. The person or team with the most points at the end of the contest will be crowned Master of Pwn, receive 65,000 ZDI reward points (instant Platinum status), a killer trophy, and a pretty snazzy jacket to boot.
Tesla vehicles are equipped with multiple layers of security, and this time around, there are three different tiers of awards within the Automotive category that correspond to some of the different layers of security within a Tesla car, with additional prize options available in certain instances.
Tier 1 earns the top prizes and represents a complete vehicle compromise. To win this level, which has the highest award amounts, a contestant will need to pivot through multiple systems in the car, meaning they will need a complex exploit chain to get arbitrary code execution on three different sub-systems in the vehicle. Success here gets a big payout as well as a new Tesla Model 3.
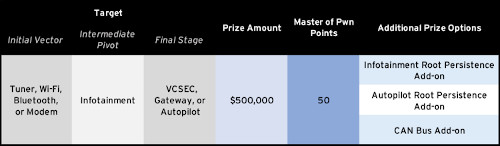
In addition to the vehicle itself and $500,000, contestants can go for the additional options to raise the payout to $700,000. This represents the single largest target in Pwn2Own history.

Tier 2 is not quite as complex but would still require the attacker to pivot through some of the vehicle’s sub-systems. This level requires the contestant to get arbitrary code execution on two different sub-systems in the vehicle, which is certainly a difficult challenge. If you include the optional targets, the largest payout for Tier 2 would be $500,000. A wining entry in Tier 2 would still be an impressive and exciting demonstration, and includes driving off with the Model 3.
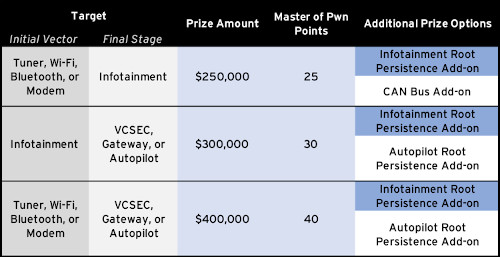
The targets in Tier 3 are just as difficult, but you only need to compromise one sub-system for a win here, which is still no easy task. Not every instance within Tier 3 includes winning the car. To drive away with a Tier 3 prize, a contestant would need to target one of the entries marked “Vehicle Included” in the table below.
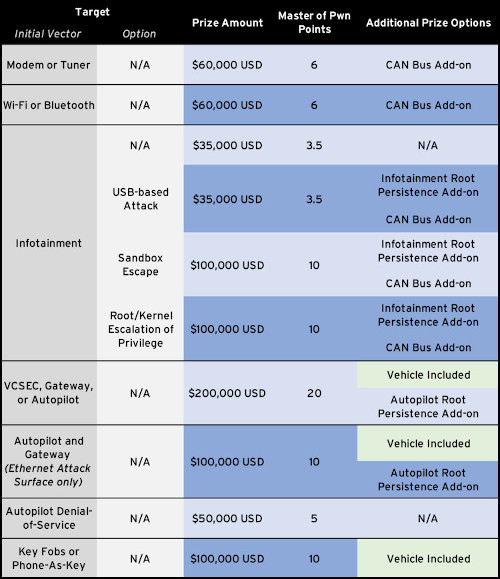
Entries against Modem or Tuner, Wi-Fi or Bluetooth, and Gateway, Autopilot, or VCSEC targets must achieve code execution by communicating with a rogue base station or other malicious entity. Entries against the Infotainment target must be launched from the target under test and must achieve code execution by browsing to malicious content. In Tier 1 and Tier 2, man-in-the-middle browser attacks against the Infotainment system are not allowed. Any Infotainment entry that leverages vulnerabilities in the built-in browser must be chained with a sandbox escape or a root/kernel privilege escalation. USB-based attacks in the Infotainment category must target the USB port that passengers would routinely plug into that is openly exposed on the center console. Any other exposed USB ports are not in scope for this contest. Entries against the Key Fobs or Phone-as-Key target must achieve code execution, arbitrary vehicle unlock, or arbitrary vehicle start using protocol-related weaknesses. Entries related to Key Fob relay or rolljam attacks are not allowed.
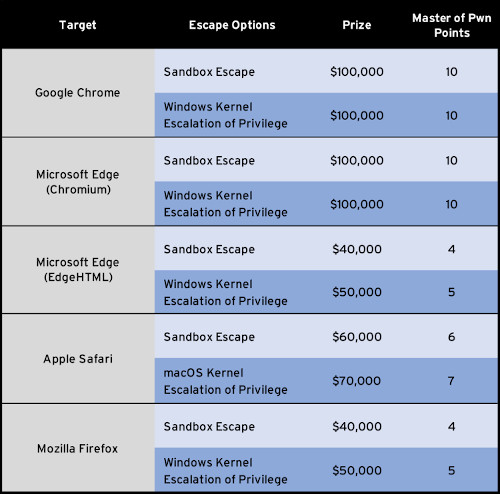
Probably the most traditional category for Pwn2Own, the Web Browser category also sees a few changes this year. Now that Microsoft Edge has both an EDGEHTML-based version and a Chromium-based version, both are included as targets. This presents an interesting opportunity – and an interesting challenge. If a single entry is able to compromise both Google Chrome and Microsoft Edge (Chromium), the contestant will receive an additional $50,000 and 5 more Master of Pwn points.
In this category, the Windows-based targets will be running in a VMware Workstation virtual machine. Consequently, all browsers except Safari are eligible for a VMware escape add-on. If a contestant is able to compromise the browser in such a way that also executes code on the host operating system by escaping the VMware Workstation virtual machine, they will earn themselves an additional $70,000 and 7 more Master of Pwn points.
The Virtualization category was introduced several years ago and continues to produce some of the most interesting research of the conference. It required an exploit escape from a virtual machine and execute code on the host OS. Microsoft Hyper-V headlines this category, with VMware Workstation, VMware ESXi, and Oracle VirtualBox as the other targets.
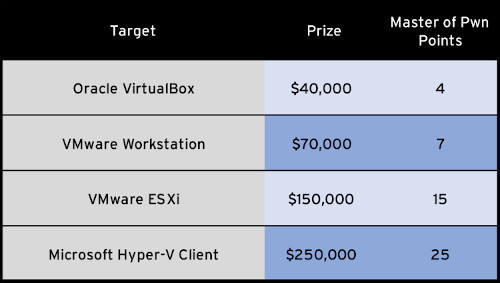
For Oracle VirtualBox, VMware Workstation, and Microsoft Hyper-V Client, both the guest and the host operating system will be running Microsoft Windows 10 19H2 x64. For VMware ESXi, the guest operating system will be running Microsoft Windows 10 19H2 x64.
There’s an add-on bonus in this category as well. If a contestant can escape the guest OS, then escalate privileges on the host OS through a Windows kernel vulnerability (excluding VMware ESXi), they can earn an additional $40,000 and 4 more Master of Pwn points.
The Enterprise Applications category includes two popular apps -- Adobe Reader and Microsoft Office 365 Plus. The Office targets will be running Microsoft Office 365 Professional Plus x64 (Monthly Channel) on Windows 10 x64. Microsoft Office-based targets will have Protected View enabled. Adobe Reader will have Protected Mode enabled.
Similar to last year, the Server-Side category contains only Microsoft Windows RDP as most of our other server-side targets are represented in our Targeted Incentive Program. If anyone brings a Bluekeep-like exploit to demonstrate, they’ll earn themselves $150,000 and 15 Master of Pwn points.
The Local Escalation of Privilege Category is one included in the past, although it has had a brief absence from the contest. This category focuses on attacks that originate from a standard user and result in executing code as a high-privileged user. This is a common tactic for malware and ransomware, so these bugs are highly relevant. In this category, the entry must leverage a kernel vulnerability to escalate privileges. The most popular operating systems are included in this category: Ubuntu Desktop and Microsoft Windows 10.
The complete rules for Pwn2Own 2020 are found here. Registration is requiredso if you are intersted, contact ZDI at zdi@trendmicro.com to begin the registration process. Registration closes at 5 p.m. Pacific Time on March 13, 2020.