Hackers Used Twitter hashtags To Extract Data From Compromised Networks
Security researchers unveiled that Russian-based hackers were using malicious software concealed in Twitter images to relay commands and steal data from US computer networks. A report by the security firm FireEye titled "HAMMERTOSS: Stealthy Tactics Define a Russian Cyber Threat Group" analyzes the functionality and obfuscation tactics of an advanced piece of malware employed by the likely Russian government-backed Advanced Persistent Threat (APT) group APT29.
Operating in its current form since at least 2014, APT29 has demonstrated very strong capabilities to adapt to, and obfuscate their activities from, network defense measures – including aggressively monitoring network defenders and/or forensic investigators and attempting to subvert them. Their discipline in operational security sets them apart even from other Russian APT groups FireEye tracks.
"The novel approach APT29 takes to carry out its attacks and maintain their persistence in networks represents a level of difficulty that security professionals could see trickle down into their own network security operations," said Laura Galante, director, threat intelligence at FireEye. "As we continue to track APT29, we will be able to bring more intelligence to light that will help our customers improve their defenses against advanced attacks."
APT29’s HAMMERTOSS is composed of multiple malware tactics to achieve its unique obfuscation goals. HAMMERTOSS follows a step-by-step retrieval of commands via common web services that would typically evade initial detection, including:
Beaconing each day to a different, algorithmically-matched Twitter handle for links and hashtags with commands;
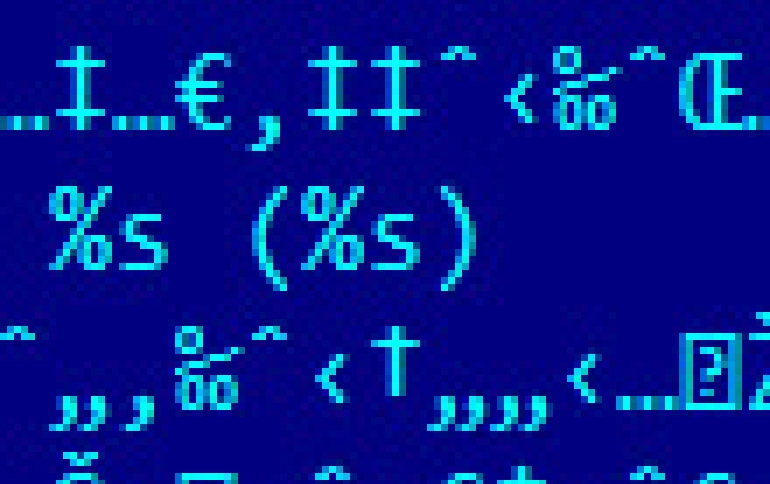
Following social media links to sites like GitHub that host images with commands hidden within them using a practice known as steganography; and
Executing commands and extracting data from the victims’ machines before uploading them to cloud storage services.
Security researchers previously linked Russian-based hacker groups to efforts to penetrate computer networks at the White House and elsewhere.
FireEye's report said this particular attack tool, dubbed "Hammertoss," generates and looks for a different Twitter handle each day and seeks to blend in with normal traffic on the messaging platform.
Inside images generated in tweets, the hackers insert malicious code that enables them to steal data or gain access to computers that view the images.
"While the image appears normal, it actually contains steganographic data," or the practice of concealing a message, image or file within another message, according to FireEye.
The technique "undermines network defenders' ability to identify Twitter accounts used for (attacks), discern malicious network traffic from legitimate activity and locate the malicious payloads downloaded by the malware," the report said.





















