Happy Shopping But Beware of Phishing
November is the first month of the busiest shopping season of the year both in China (Singles’ Day) and elsewhere (Black Friday, Cyber Monday), so cybercriminals are also getting ready for phising attacks.
Singles’ Day in China begins on 11.11 and has morphed into one of the largest online (and offline) shopping days in the world. This year's Black Friday falls on November 23rd this year. It’s a great time for shoppers, but many people drop their guard and become the easy prey of cybercriminals.
In recent years financial phishing has made up at least a quarter of all annual phishing attacks. According to Kaspersky, in 2017, financial phishing exceeded half of the attacks. Safe to say, we can assume that this upward trend will continue for the rest of 2018.
Kaspersky's stats indicate that during this period, financial phishing accounts for an additional 10% share of all attacks. Outside the sale season, fraudsters favor banking clients.
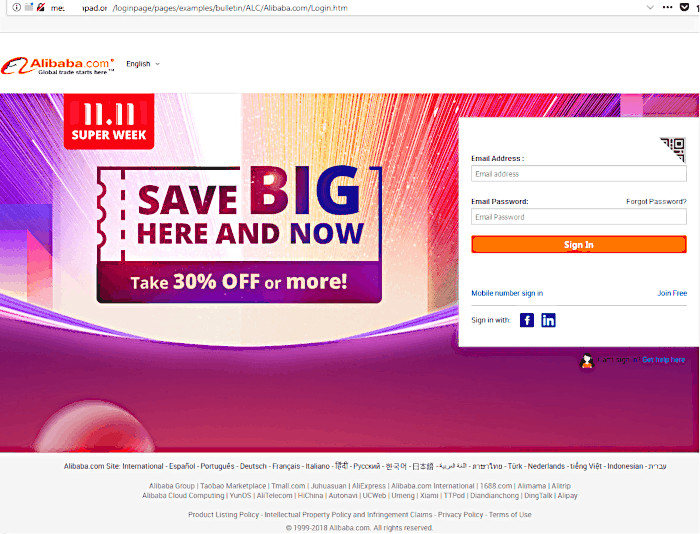
On Singles’ Day, the cybersecurity research firm saw a spike in the number of attempts blocked by our security solutions to redirect users from dangerous resources. An upswing was recorded on November 9th, which is not surprising given that cybercriminals always start preparing in advance. Mass attacks are usually carried out shortly before the actual date of the sell-off. Phishing attacks against clients of Alibaba Group, the main player in Singles’ Day, had sharp hike upwards, about double compared to the average number of attacks in November.
How phising look like? Just have a look at the screenshot below, which depicts two websites using standard social engineering techniques: multiple mentions of "alibaba" in the URL to confuse inattentive or naive users, a copy of the company’s logo to add authenticity, and a flashy picture to divert attention.

US online giant, Amazon, matches Alibaba stride for stride in terms of both sales/promotions and cybercriminals looking to create fake versions of company sites.

Cybercriminals tend to use a similar formula on phishing attacks. Lucrative offers are first used as bait. But before the users can access the deal, they are instructed to fill out a form that asks for all their personal details. Address, phone number, etc. Once the form is completed, users are prompted to forward the link to their friends. Needless to say, the user never gets the deal: The victim is simply transferred from site to site, with countless pointless surveys.
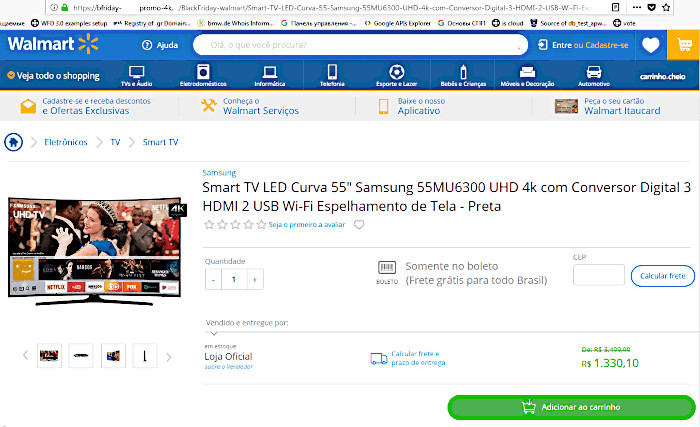
There is a large number of registered (and thus far, dormant) sites like blackfridayscom.tld and black-fridaywalmart.tld. In the run-up to Black Friday, these websites are filled with content by cybercriminals looking to harvest personal and banking details of unsuspecting shoppers.
As a matter of fact, Kaspersky has started to see phishing activity for Black Friday 2018. Fraudsters have started to send out mass phishing e-mails leading to fake sites, impersonating stores that currently offer Black Friday specials.
The domain name of this fake store posing as Walmart speaks volumes about the event it was created for. The site follows the typical phishing formula. It hooks consumers with an irresistible price on a brand new TV. Once the checkout process begins, consumers obligingly fill out forms with their confidential data and unknowingly send payment to a private online wallet.
In regards to phishing e-mails, Kaspersky found a fake Black Friday promotion offering a free two-month subscription to Netflix. Users who want to redeem the promotion are directed to a scam Netflix site, which prompts them to enter their credit card information and other personal information. This data goes to the attackers, while the victim of the fraud receives nothing in return. Instead of a free Netflix subscription, the user gets their bank account hacked.
Also ahead of Black Friday, various fake online stores are set up, offering mouth-watering discounts on global brands. This means that if something online sounds too good to be true, it most likely is.
In order to understand if a store is real or fake, avoid stores registered on free hosting services. You should also carefully study the URLs of pages with forms requesting confidential data. If the address consists of a meaningless set of characters or the URL looks suspicious, do not proceed with payment.
If the store website arouses any sort of suspicion, look up the site on WHOIS for information about how long the domain has existed and who owns it. If the domain is fresh and registered to some mystery entity, take your business elsewhere.
In any case, when you are shopping onlime, get yourself a special card for online purchases and don’t keep large sums of money on it. Don’t visit shopping sites from links in e-mails, social media messages, and chat rooms, or by clicking/tapping advertising banners on suspicious sites. Try to avoid using public Wi-Fi hotspots for shopping purposes unless you use a a VPN. And before entering personal information, make sure that you are on the genuine site. The address bar should contain the correct URL, preceded by the letters "https" and/or a green padlock. If so much as one character in the domain name is wrong, don’t even think about entering any confidential data.