Google Chrome Updates Bring DNS over HTTPS, Blocking of Mixed HTTPS Pages
Google plans to introduce controversial DNS over HTTPS (DoH) to Chrome along with another HTTPS change that is set to hit the hundreds of millions using the web browser.
The DNS over HTTPS (DoH) essentialy bypasses local DNS nameservers, sending encrypted traffic to a central server instead.
Google has prompted U.S. lawmakers to raise concerns over plans to enhance user privacy and security by introducing encrypted web addresses. The concern is that such a move will keep consumer data from Google’s competitors and put even more user information in its own grasp.
Encrypting thetraffic cuts out the current middle layer of ISPs, cable carriers and wireless networks.
For its part, Google has assured that it has "no plans to centralize or change people's DNS providers to Google by default."
Mozilla has also announced similar plans for Firefox, saying that “after many experiments—we feel confident that enabling DoH by default is the right next step.” The company claimed “most of our users will benefit from the greater protections of encrypted DNS traffic,” but assured that “when DoH is enabled, users will be notified and given the opportunity to opt out.”
Google is also gradually start ensuring that https:// pages can only load secure https:// subresources. Chrome will start blocking mixed content (insecure http:// subresources on https:// pages) by default.
HTTPS pages commonly suffer from a problem called mixed content, where subresources on the page are loaded insecurely over http://. Browsers block many types of mixed content by default, like scripts and iframes, but images, audio, and video are still allowed to load, which threatens users’ privacy and security. Google says that loading mixed content also leads to a confusing browser security UX, where the page is presented as neither secure nor insecure but somewhere in between.
In a series of steps starting in Chrome 79, Chrome will gradually move to blocking all mixed content by default. To minimize breakage, Google will autoupgrade mixed resources to https://, so sites will continue to work if their subresources are already available over https://. Users will be able to enable a setting to opt out of mixed content blocking on particular websites.
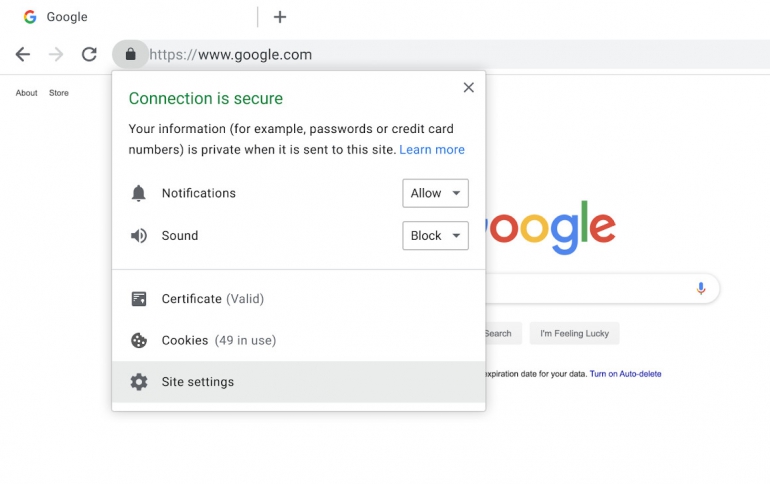
In Chrome 79, releasing to stable channel in December 2019, Google will introduce a new setting to unblock mixed content on specific sites. This setting will apply to mixed scripts, iframes, and other types of content that Chrome currently blocks by default. Users can toggle this setting by clicking the lock icon on any https:// page and clicking Site Settings. This will replace the shield icon that shows up at the right side of the omnibox for unblocking mixed content in previous versions of desktop Chrome.
In Chrome 80, mixed audio and video resources will be autoupgraded to https://, and Chrome will block them by default if they fail to load over https://. Chrome 80 will be released to early release channels in January 2020. Users can unblock affected audio and video resources with the setting described above.
Also in Chrome 80, mixed images will still be allowed to load, but they will cause Chrome to show a “Not Secure” chip in the omnibox.
In Chrome 81, mixed images will be autoupgraded to https://, and Chrome will block them by default if they fail to load over https://. Chrome 81 will be released to early release channels in February 2020.
Google will also offer resources to developers to hunt out miscreant content on their own sites and apply fixes. The approach Google takes to encryption is to work with developers to push them onto HTTPS.
Google has already shifted from flagging secure sites to users to doing that the other way around, essentially badging HTTP as “not secure,” so users can be in no doubt.





















