
Browsers' Password Managers Are Used by Advertisers' Scripts For Tracking Sites
Web browsers' built-in password managers is abused by third-party scripts for tracking on more than a thousand sites, according to researchers.
Nearly every web browser now comes with built-in login managers (also called password managers). According to a new research from Princeton's Center for Information Technology Policy, third-party scripts exploit thsese password managers to retrieve and exfiltrate user identifiers without user awareness.
The underlying vulnerability of login managers to credential theft has been known for years.
The researchers haven't found password theft on the 50,000 sites that they analyzed, but they found tracking scripts embedded by the first party abusing the same technique to extract emails addresses for building tracking identifiers.
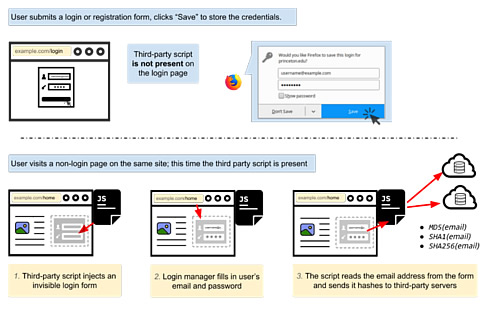
Here is how it works: First, a user fills out a login form on the page and asks the browser to save the login. The tracking script is not present on the login page. Then, the user visits another page on the same website which includes the third-party tracking script. The tracking script inserts an invisible login form, which is automatically filled in by the browser's login manager. The third-party script retrieves the user's email address by reading the populated form and sends the email hashes to third-party servers.
The researchers examined two different scripts - AdThink and OnAudience - both of are designed to get identifiable information out of browser-based password managers. The scripts work by injecting invisible login forms in the background of the webpage and scooping up whatever the browsers autofill into the available slots. That information can then be used as a persistent ID to track users from page to page, a potentially valuable tool in targeting advertising.
According to the researchers, there's no technical measure to stop scripts from collecting passwords. The only fix would be to change how password managers work, requiring more explicit approval before submitting information.













