IBM Prevents Insider Attacks
IBM unveiled on Monday its new software designed to help companies prevent attacks from the inside on their IT systems mostly designed for businesses.
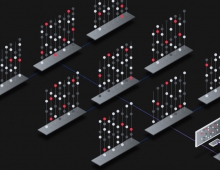
The new Big Blue's Identity Risk and Identification software monitors user actions and searches for unusual behaviour. The application analyses the past actions of every employee and compares their activities with normal activity patterns for their co-workers.
Insider attacks, such as employees stealing confidential information, represent a growing category of security incident, IBM claimed.
According to an IBM study published last month, 56 per cent of organisations have reported a security breach from within their company.
"Companies desperately need an effective solution that can adapt to the ever-changing world of fraud and theft," said William Pulleyblank, a vice president at IBM's Center for Business Optimization which developed the system.
"A key feature of this new solution is its ability to continually update the behaviour detection model with newly acquired intelligence based on changing business situations. This creates an "adaptive identity analysis" which allows the technology to automatically adapt the parameters for suspicious behaviour."
Insider attacks, such as employees stealing confidential information, represent a growing category of security incident, IBM claimed.
According to an IBM study published last month, 56 per cent of organisations have reported a security breach from within their company.
"Companies desperately need an effective solution that can adapt to the ever-changing world of fraud and theft," said William Pulleyblank, a vice president at IBM's Center for Business Optimization which developed the system.
"A key feature of this new solution is its ability to continually update the behaviour detection model with newly acquired intelligence based on changing business situations. This creates an "adaptive identity analysis" which allows the technology to automatically adapt the parameters for suspicious behaviour."